Published: April 24, 2026 at 12:04 pm
Updated on April 24, 2026 at 1:39 pm

A digital signature in Web3 is a cryptographic proof that verifies the authenticity and integrity of a digital message or transaction. It acts like a secure, unforgeable handwritten signature, but powered by mathematics instead of ink.
In the decentralized world of Web3, digital signatures replace traditional login systems and centralized trust. They prove that you — and only you — authorized a specific action using your private key, without ever revealing it. This makes them the foundation of blockchain security, transaction validation, and user authentication across decentralized applications (dApps).
Digital signatures rely on asymmetric cryptography, also known as public-key cryptography. Each user has two mathematically linked keys:
This pair enables three critical security properties:
Here’s a simplified breakdown of how digital signatures work in Web3:
This process combines hash functions and encryption to guarantee both who sent the data and that it hasn’t been tampered with.
Most blockchains, including Bitcoin and Ethereum, use the Elliptic Curve Digital Signature Algorithm (ECDSA) with the secp256k1 curve. ECDSA is efficient, secure, and produces compact signatures.
In Ethereum, a signature consists of three values: r, s, and v (recovery id). Smart contracts can verify signatures on-chain using the built-in ecrecover function, which recovers the signer’s address from the signature and message hash.
Digital signatures power almost everything users do in Web3:
Digital signatures bring several powerful advantages to the decentralized web:
Compared to traditional electronic signatures, blockchain-based digital signatures offer immutable audit trails and true decentralization.
Despite their strengths, cryptographic signatures in Web3 face real challenges:
In Ethereum, every transaction you send is signed using ECDSA. Popular wallets like MetaMask handle signing transparently.
Projects like Sign-In with Ethereum (SIWE) standardize message signing for seamless logins across dApps. NFT marketplaces use signatures for lazy minting, while DeFi protocols use them for off-chain orders that are later settled on-chain.
Other blockchains (Solana, Cosmos, etc.) use similar cryptographic primitives, though with different signature schemes in some cases.
Best practices include:
What is a digital signature in Web3?
A digital signature in Web3 is a cryptographic proof created with your private key that verifies you authorized a message or transaction while ensuring the data remains unchanged.
How do digital signatures work with private and public keys?
You sign data with your private key. Anyone can verify it using your public key. The signature proves ownership without revealing the private key.
What is ECDSA in blockchain?
ECDSA (Elliptic Curve Digital Signature Algorithm) is the most common algorithm used in Ethereum and Bitcoin to create and verify digital signatures efficiently and securely.
Can someone forge a digital signature?
No — forging a valid signature without the private key is computationally infeasible with current technology, thanks to the hardness of the elliptic curve discrete logarithm problem.
What happens if I sign a malicious message?
Signing can approve unwanted actions (e.g., draining funds). Always verify the exact content and origin before signing.
Are digital signatures legally binding in Web3?
In many jurisdictions, cryptographic signatures can have legal weight, especially when combined with blockchain timestamps and legal wrappers. However, laws vary by country.
What’s the difference between signing a transaction and signing a message?
Transaction signing moves assets or changes on-chain state and costs gas. Message signing is off-chain, gasless, and mainly used for authentication or permissions.
As Web3 evolves, we’re seeing improvements in account abstraction (making signing more user-friendly), post-quantum cryptography, and cross-chain signature standards. Digital signatures will remain the cornerstone of trust and identity in the decentralized internet.
The concept of digital signatures in Web3 represents a fundamental shift from centralized trust to cryptographic proof. By enabling secure, verifiable, and decentralized authentication, digital signatures power transactions, logins, governance, and ownership across the blockchain ecosystem.
Understanding how they work — from public-private key pairs to ECDSA and message signing — is essential for anyone participating in Web3. Whether you’re a user protecting your assets or a developer building the next dApp, mastering digital signatures is key to navigating the decentralized future safely and confidently.
Related Topics





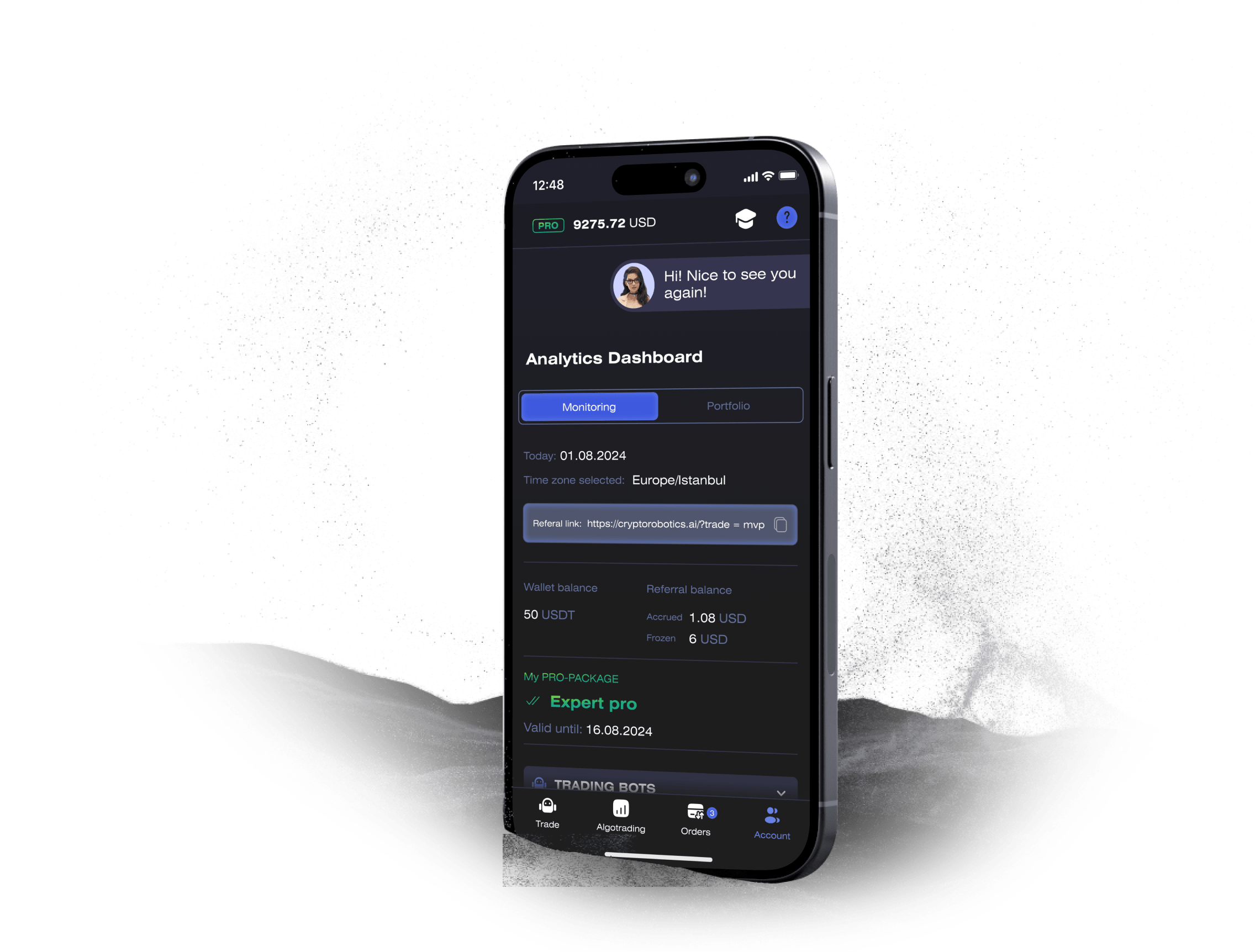
Access the full functionality of CryptoRobotics by downloading the trading app. This app allows you to manage and adjust your best directly from your smartphone or tablet.
News
See more



Blog
See more


