Published: November 23, 2024 at 11:18 pm
Updated on November 23, 2024 at 11:18 pm



With the rise of digital currencies, transaction security is more crucial than ever. Blockchain technology is at the forefront, providing a secure environment for our increasingly online lives. This article explores some of the innovative protocols ensuring our transactions are safe, focusing on Omnia and LayerZero while also considering established players like Chainlink CCIP.
Decentralization is one of those buzzwords that gets thrown around a lot in crypto circles, but it’s foundational to how blockchains work. By spreading data across a network of nodes instead of relying on a single central authority, decentralization enhances reliability and makes systems resistant to censorship. Even if some nodes fail or get compromised, the data remains intact because it’s replicated across multiple locations.
This structure also makes it incredibly difficult for any single entity to manipulate or censor transactions. Without a central point of control, decentralized networks operate on a peer-to-peer basis where miners or validators collectively validate and add transactions to the blockchain. This not only enhances security but also minimizes the risk of data breaches since there’s no single point of failure.
At the heart of blockchain technology lies cryptography. It secures transactions through complex mathematical algorithms that ensure only authorized parties can access transaction data. Public and private keys are fundamental; public keys are shared openly while private keys remain confidential.
Hash functions further enhance security by creating unique fingerprints for each transaction, making any alteration immediately apparent. These cryptographic principles underpin popular blockchains like Bitcoin and Ethereum, allowing them to operate without centralized authorities while maintaining user trust.
Consensus protocols are essential for any blockchain network as they ensure all participants agree on its state. Common types include Proof of Work (PoW), Proof of Stake (PoS), and Practical Byzantine Fault Tolerance (PBFT). Bitcoin uses PoW, where miners solve complex puzzles to validate transactions; Ethereum is transitioning to PoS with its 2.0 upgrade, which locks validators’ tokens as collateral.
Each consensus method has trade-offs regarding energy consumption, speed, and security—PoW is costly but highly secure, while PoS is more efficient yet potentially vulnerable under certain conditions.
Smart contracts—self-executing agreements coded into blockchains—have become integral to many decentralized applications (dApps). However, their complexity has led to numerous exploits over the years. Companies like ConsenSys Diligence perform thorough audits to identify vulnerabilities before deployment.
Standardized coding practices and protective measures against known attack vectors are vital for maintaining smart contract security as their usage continues to expand.
Bitcoin remains the gold standard for transaction security due to its focus on decentralization and transparency. Its PoW consensus mechanism effectively prevents double-spending and fraud; however, it requires significant energy resources.
Ethereum’s flexibility allows for innovative use cases involving smart contracts that enhance transactional security by automating processes between parties without intermediaries. Its transition to PoS aims at increasing efficiency while reducing environmental impact.
Ripple specializes in real-time gross settlement systems that facilitate cross-border payments securely and efficiently through an independent validator consensus algorithm that confirms transactions almost instantaneously.
Litecoin operates similarly to Bitcoin but employs different cryptographic techniques via its Scrypt proof-of-work algorithm which requires distinct computational resources thus preventing attacks through alternative means available in Bitcoin’s case.
Cardano takes an academic approach towards developing its blockchain ecosystem utilizing Ouroboros—a proof-of-stake protocol designed with rigorous peer-reviewed research ensuring high levels scalability alongside robust security features integrated within layered architecture separating operational components from settlement layers safeguarding them effectively against potential threats posed by malicious actors targeting less fortified structures susceptible exploitation therein.
Ensuring safe transactions involves both user authentication practices coupled with robust network securities guarding against external interferences attempting disrupt integrity thereof.
Authentication methods securing users identity prior authorizing actions within system are paramount. Multi-factor authentication combining passwords alongside secondary verification channels such SMS codes biometric scans provide additional layers protection. Hardware wallets storing private keys offline shield them phishing attempts prevalent among unsuspecting users unaware dangers lurking cyberspace.
Network securities employing firewalls intrusion detection systems detecting unauthorized entries encrypting sensitive information traversing networks via TLS protocols constitute fundamental safeguards protecting integrity confidentiality availability data residing therein.
Blockchain technologies continue evolving improving upon existing paradigms emerging new ones addressing contemporary challenges facing ecosystems today. Zero-knowledge proofs homomorphic encryption offer possibilities handling confidential information without revealing underlying datasets whilst quantum-resistant encryptions garner attention counteracting potential threats posed current standards rendered obsolete by advances computing capabilities.
Newly developed protocols such as Omnia LayerZero Cosmos IBC cater diverse needs securing interconnectivity between disparate chains. Omnia focuses front-running prevention utilizing private endpoints blocking transaction data, whereas LayerZero enables cross-chain messaging facilitating seamless exchanges information across multiple platforms, finally Cosmos IBC provides secure interchange facilitating efficient transfers diverse ecosystems ensuring safety integrity all participants involved therein.
As blockchain technology matures so do its requirements developers business leaders alike continuously researching innovating solutions meet demands ever-growing complexities landscapes they inhabit. With advancements come better defenses against malicious actors seeking exploit vulnerabilities present systems paving way more reliable trustworthy crypto market platform future ahead us all.
CryptoRobotics is committed to delivering transparent and reliable reporting in alignment with the principles upheld by the Trust Project. Every element within this news piece is meticulously crafted to uphold accuracy and timeliness. However, readers are encouraged to conduct independent fact-checking and seek advice from qualified experts before making any decisions based on the information provided herein. It's important to note that the data, text, and other content presented on this page serve as general market information and should not be construed as personalized investment advice.
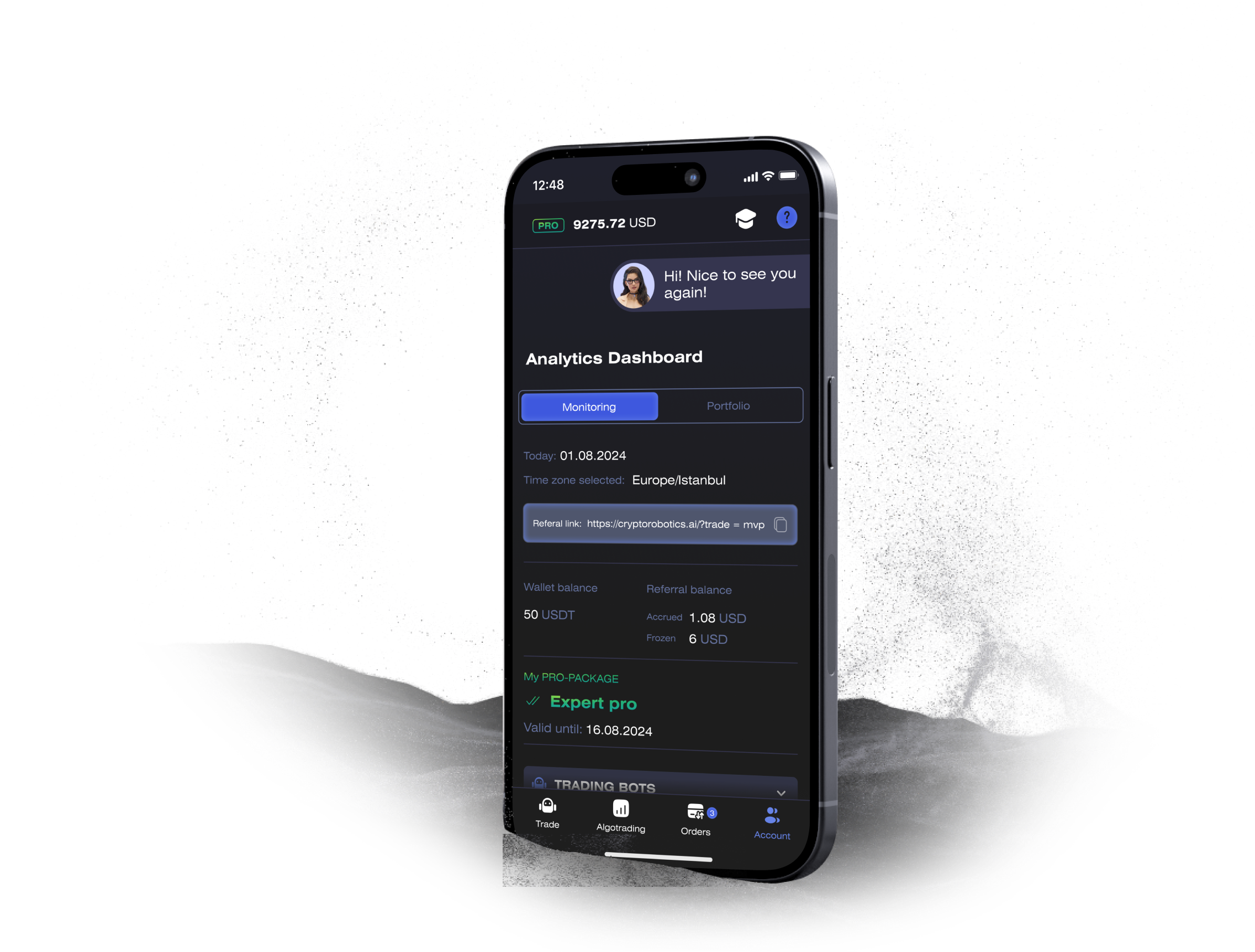
Access the full functionality of CryptoRobotics by downloading the trading app. This app allows you to manage and adjust your best directly from your smartphone or tablet.
News
See more


